Enorasys
Athens, Greece




Encode helps businesses effectively manage advanced cyber attacks. Enorasys, its security analytics and response orchestration platform, enables timely detection of cyber threats and effective targeted response against cyber threat actors and APT attacks.
All CustomersProduct Development
Having combined Encode’s cybersecurity expertise with our software development prowess, we extended the functionality of their security and response orchestration platform, performed comprehensive API refactoring, and switched to a better-performing database.
Learn moreStartups & Innovation
We help companies innovate faster by implementing modern and easily scalable solutions to future-proof their products. For Encode, partnering up with Redwerk resulted in an upgraded, well-tested platform that is easy to build on and maintain in the future.
Learn moreChallenge
Our major task was to help Encode upgrade one of their products, namely,Enorasys Security Analytics. This SaaS platform is a proprietary software “designed by security analysts for security analysts.” Having combined the power of machine learning and Encode hands-on offensive and defensive security expertise, this platform allows businesses to detect any security compromises early on, monitor suspicious activities and patterns, and trace the origin of the attack.
Encode had a clear vision of how they could upgrade their platform and fine-tune the entire infrastructure to improve their service quality and faster cater to their clients’ needs. However, to achieve the set milestones within a shorter time, they needed someone with hands-on experience in developing, enhancing, and maintaining innovative SaaS products. Redwerk turned out to be a perfect match.
As a cybersecurity services provider, Encode prioritizes the quality of its software, ensuring it’s robust, compliant with the latest software development and security standards, and running 24/7.
On top of that, Encode wanted to future-proof their product and prevent any challenges associated with rapid data growth, lack of software scalability, and rising cost of maintaining their IT infrastructure.
To help Encode achieve those goals, we were tasked with codebase refactoring, performing migration to Elasticsearch and making it the primary data warehouse, and implementing a multitenant architecture. We were also engaged in updating and expanding current unit and integration tests.
Solution
Being an IBM-recognized leader in cyber threat management, Encode takes care not only of their clients’ security but also follows strict security controls when it comes to cooperating with external vendors. For this reason, all code development, debugging, and testing from our end was performed on a remote workstation.
The bulk of our development efforts was aimed at refactoring and switching to Elasticsearch as the main data storage instead of MySQL + Splunk. The intricacy lay in that we had to translate business logic and complex algorithms for calculating metrics using a new database. This, in turn, quite often caused difficulties in implementation since the required dataset could still be partly stored in MySQL. Another hindrance was that in Elasticsearch, the data aggregation might not be implemented in the same way. Therefore, we had to look for alternative solutions.
We also had to use only the latest version of Elasticsearch and contribute to the official Python libraries (bucket sort aggregation patch, generating Swagger specification fix, resource grouping fix) that struggled to fully support the new functionality as quickly as we needed.
Another deliverable we shipped is the system’s Audit Log. The latter is a crucial piece of the platform’s functionality, especially from a cybersecurity standpoint. Providing records of all activity, including suspicious activity, Audit Log helps detect vulnerabilities before advanced persistent threats are put in place, track malicious performance, and enhance overall security.
The new version we were working on also presupposed an upgrade in how Encode provides their services to clients. For that, we designed and implemented a multitenant architecture. In the previous version, it was necessary to supply each client with its own instance of the application. In contrast, in the new version, all clients can be served by a single instance with complete data isolation. This greatly simplifies delivery and regular updates to the product’s latest version and significantly reduces infrastructure costs.
One more must-have feature we implemented is a role-based access control system (RBAC). It provides more flexibility in the selective management of access to resources. Moreover, RBAC allows Encode to improve operational efficiency, enhance compliance, optimize resource use, and decrease the risk of data breaches and leakage.
We also reworked and improved the app configuration module.
Lastly, we updated and expanded all the available unit tests and introduced integration testing. Products like Enorasys require a doubled amount of testing, so we made sure QA can be performed on a decent level.
Result
Our partnership with Encode turned out to be mutually enriching. While we gained new expertise in the cybersecurity sector and contributed to open source libraries, Encode received a set of high-quality solutions aimed at uplifting their security analytics and response orchestration platform:
- Successful API refactoring
- Smooth data aggregation in NoSQL
- Business logic optimization
- Upgraded functionality
- Extended collection of unit and integration tests
Awarded
Looking for a tech partner to upgrade your product?
Contact UsTechnologies
Redwerk Team Comment

Dmitry
Software Developer
I worked on this project with immense pleasure, and it turned out to be a fantastic experience for the entire dedicated team. The codebase version we were to refactor and upgrade was well-written and thoroughly documented. The software development management and all workflows were streamlined as well. Encode provided us with excellent specialists who answered all our questions, participated in the demo, and conducted a high-quality code review. It is worth noting that in solving some problems, we had a chance to communicate on forums and bug trackers with leading developers, as well as contribute to opensource.
Impressed?
Hire usOther Case Studies
Platform Upgrade For European Parliament
Upgraded the European Parliament's e-voting platform in less than a month
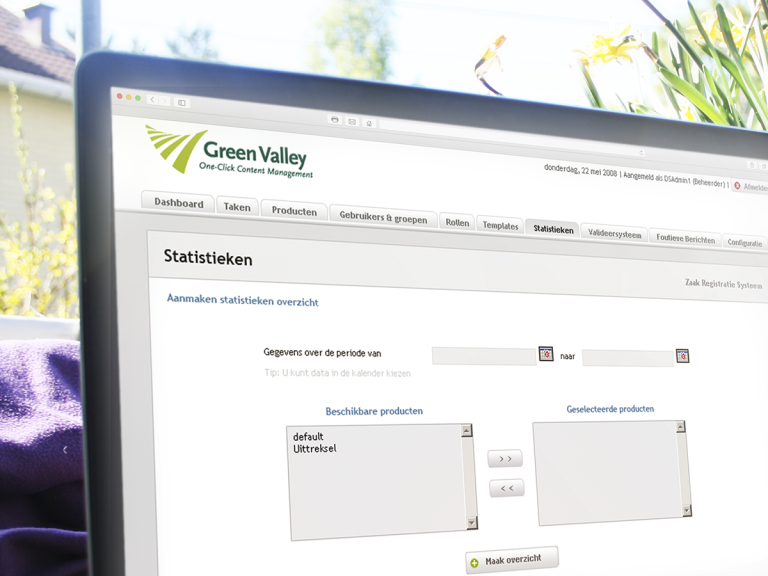
Web Intake
Developed a management software for citizens’ requests, which is used by 50% of city councils in Belgium and the Netherlands